Blogs
Recent Posts
Project Ares Students: a conversation with Nicole Mendoza
Nicole Mendoza – alumna of the SacCARES (Sacramento Cares) cybersecurity Accelerator at Inteligenca – discussed turning the COVID crisis into a time of opportunity.

8 Tips to Keep Your Small Business Cyber Safe this Holiday Season
The holiday season is a time of giving, however, for hackers it can be a time of swindling. We are all susceptible to cyberattacks, but

Project Ares Updates for the Back-to-School Season
We have a virtual backpack full of new supplies for teaching and learning with Project Ares. Check out the capabilities that make it easier for

Transitions to the Cloud: Considerations for Cyber Training and Readiness
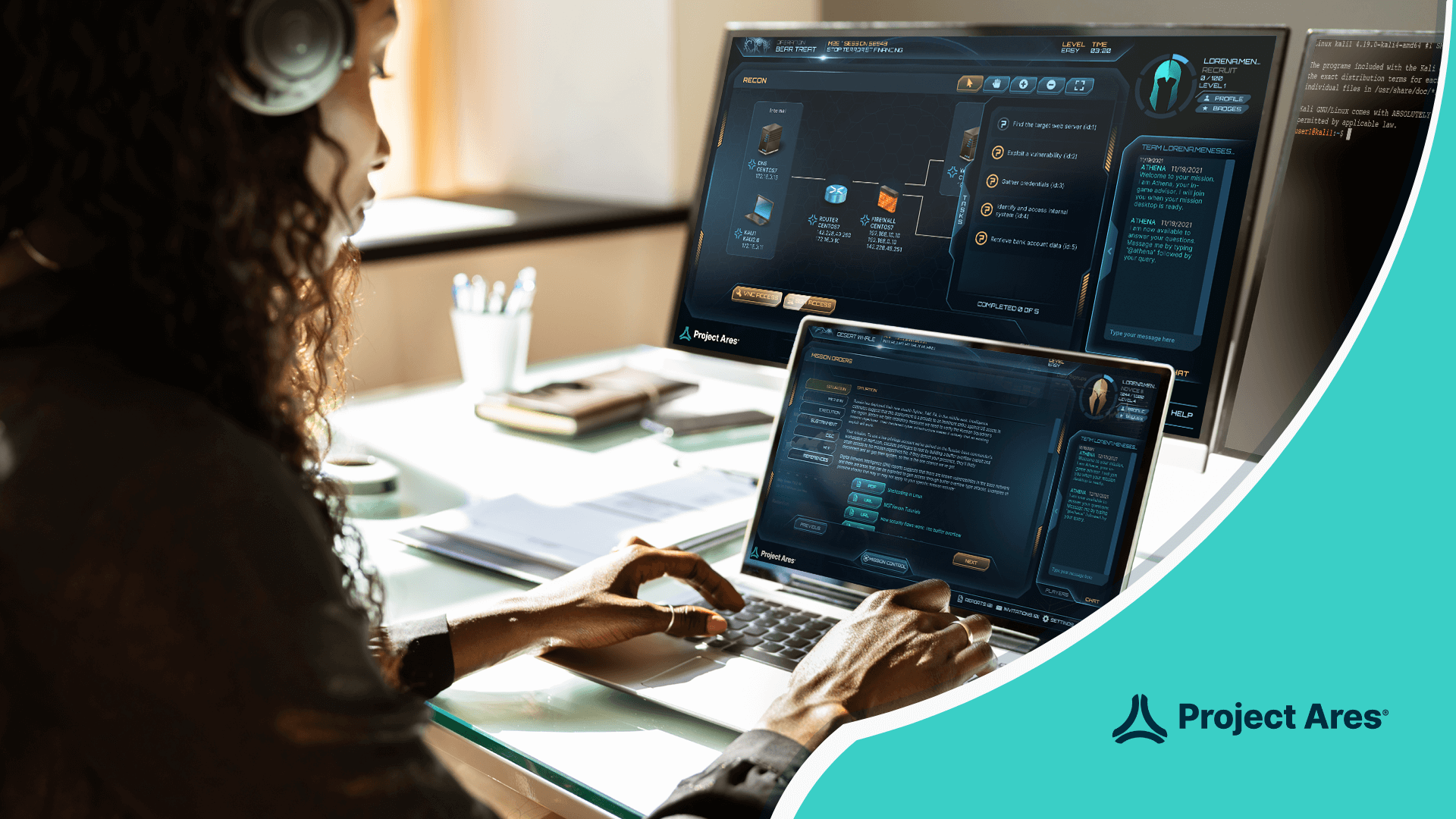
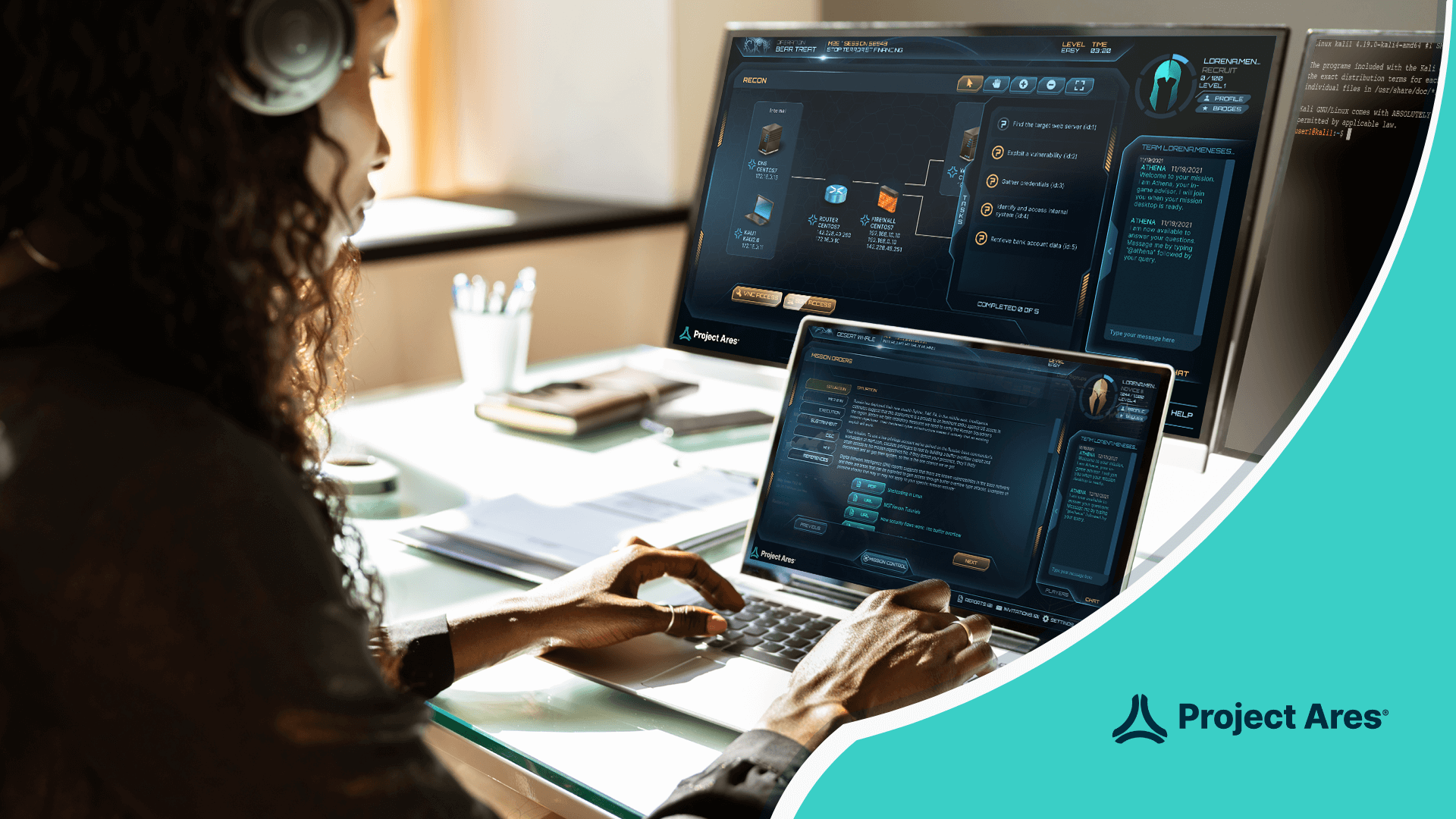
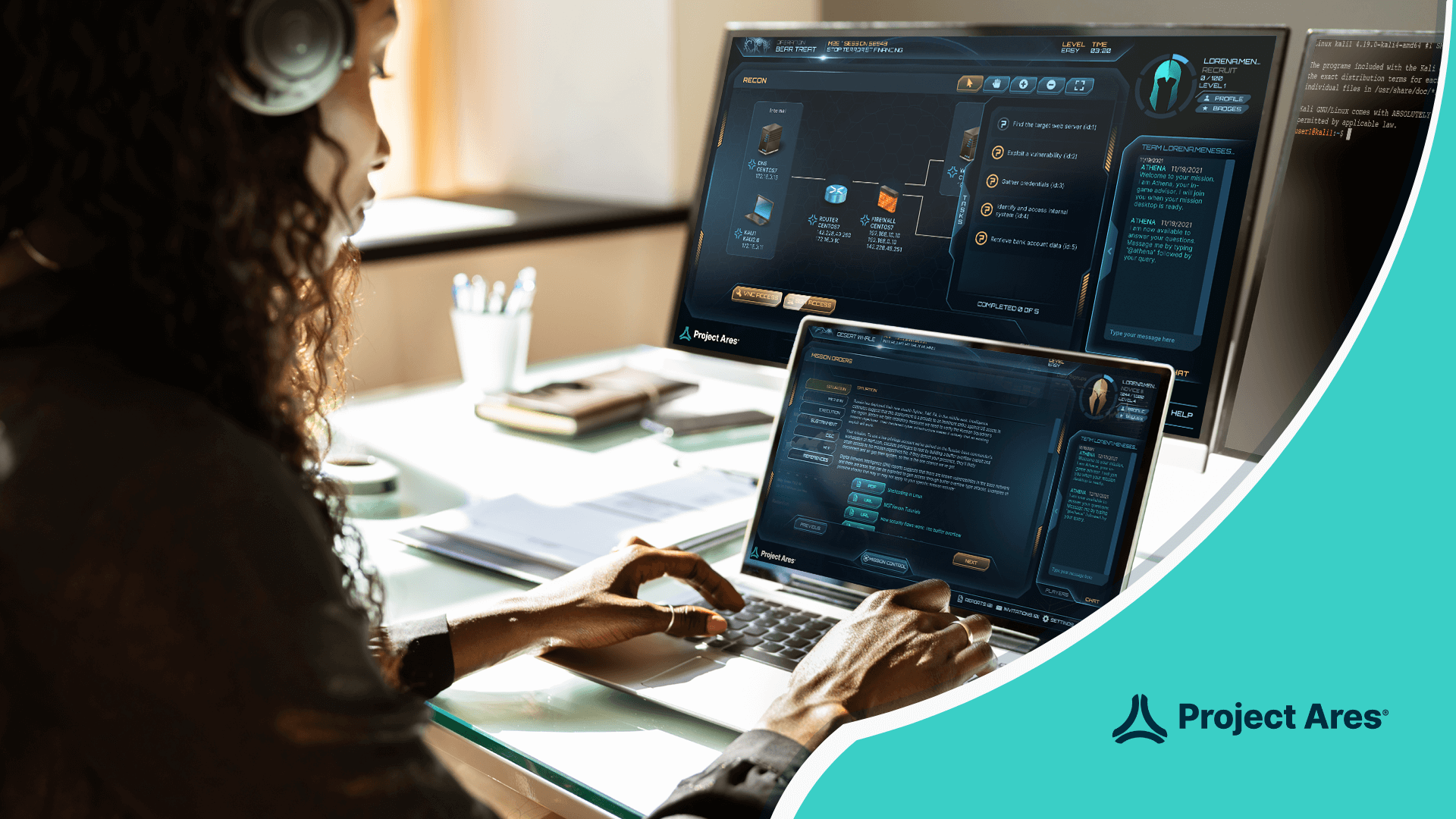
Hands on webinar with Project Ares, our gamified, realistic cybersecurity education platform
All Posts

Transitions to the Cloud: Considerations for Cyber Training and Readiness
Hands on webinar with Project Ares, our gamified, realistic cybersecurity education platform

8 Tips to Keep Your Small Business Cyber Safe this Holiday Season
The holiday season is a time of giving, however, for hackers it can be a time of swindling. We are

Cyber Monday and Black Friday Tips to Prevent Holiday Hacks
If you’re anything like me, you get really excited when the holidays roll around. The music is cheerful (the Hallmark

Cybersecurity in the Age of Digital Transformation
From unifying security architecture to automating routine security tasks to building a culture of continuous cyber training for professionals, Circadence

6 Cybersecurity Teaching Best Practices To Show You How To Use Project Ares Labs Like A Gym
Welcome to the Project Ares Training Ground! Here, we believe in putting cyber readiness in the hands of learners –
Project Ares Students: a conversation with Nicole Mendoza
Nicole Mendoza – alumna of the SacCARES (Sacramento Cares) cybersecurity Accelerator at Inteligenca – discussed turning the COVID crisis into

Project Ares Students: a conversation with Ken Perez
Ken Perez – an alum of the SacCARES (Sacramento Cares) Cybersecurity Accelerator from our Project Ares partners at Inteligenca – discusses
Project Ares Students: a conversation with Robert Hogan
Project Ares Team talks with Robert Hogan about his cybersecurity education pursuits and the inspiration that led him to Project

From Student to Instructor: A Cybersecurity Learning Journey
One person’s cybersecurity learning journey from an oil and gas technician to a cybersecurity instructor.

6 Common Mistakes in the Project Ares Gym
Is there a wrong way to “do the gym”? In our experience, every uncertainty encountered in the Project Ares gym

Why You Need a Cyber Training Plan (& Which to Choose!)
In every gym, you’ll find a variety of Personal Trainers. The Project Ares cyber gym is no different! As a

The Ultimate Trainer’s Guide to the Project Ares Cyber Gym
Project Ares is a cyber-gym that’s chock-full of digital treadmills, virtual weight racks, and high-tech yoga mats designed to help